As cryptocurrency adoption grows, so does the variety of scams concentrating on unsuspecting customers. In 2025, one of the vital regarding developments has been the rise of Crypto Drainers-as-a-Service (DaaS), a brand new breed of cybercrime that makes it simpler than ever for scammers to steal digital property.
Drainers are malicious instruments designed to empty crypto wallets by tricking customers into approving transactions that give scammers entry to their funds. What makes Crypto Drainers-as-a-Service particularly harmful is that it permits anybody, even these with little technical talent, to launch these assaults. For a payment, you should purchase or lease drainers on the darkish net or Telegram teams, full with easy-to-use dashboards, phishing templates, and even buyer help.
On this article, we’ll break down how Crypto Drainers-as-a-Service works, who’s utilizing them, and most significantly, how one can defend your self from turning into a sufferer.
How does DaaS work as a plug-and-play rip-off toolkit?
Crypto Drainers-as-a-Service (DaaS) function like pre-packaged rip-off toolkits, providing cybercriminals a fast and simple option to steal digital property. These kits include ready-to-use phishing web sites, faux pockets interfaces, and scripts that exploit pockets permissions, significantly on Ethereum and different EVM-compatible blockchains.
Right here’s the way it usually works:
The scammer pays to entry a drainer service or subscribes to a revenue-sharing mannequin.
They’re given a phishing template mimicking standard dApps, NFT mints, or crypto companies.
Victims are lured to the phishing website through faux adverts, social media posts, Discord messages, or compromised verified accounts.
As soon as a person connects their pockets and unknowingly indicators a malicious transaction, the drainer script is triggered, instantly transferring the contents of the pockets to the scammer’s tackle.
DaaS vs. Conventional Crypto Scams
Crypto Drainers-as-a-Service (DaaS) differ from conventional crypto scams in supply technique, execution pace, and much extra:
[Insert Image 1]
Whereas conventional phishing depends on tricking victims into giving up login credentials, DaaS kits exploit the best way wallets deal with good contract permissions. This makes them sooner and, in lots of circumstances, more durable for common customers to detect earlier than it’s too late.
How These Scams Function
DaaS usually mimic reputable Web3 initiatives, NFT mints, or standard DeFi platforms. Right here’s how they usually unfold:
Step-by-Step of a DaaS Rip-off
Phishing Hyperlink or Faux Web site
The crypto rip-off begins when the attacker distributes a phishing hyperlink through compromised social media accounts, Discord channels, faux adverts, or direct messages. These hyperlinks result in web sites that completely mimic reputable platforms (like NFT mint pages or DeFi dashboards).
Sufferer Connects Their Pockets
As soon as on the positioning, the unsuspecting person is prompted to attach their crypto pockets. The whole lot seems regular. The location could even have countdown timers or buzzwords like “unique drop” to create urgency.
Malicious Sensible Contract Execution
After the pockets is linked, the positioning methods the person into signing a transaction. However as an alternative of minting an NFT or claiming a token, the person is unknowingly giving the attacker permission to entry or switch funds from their pockets.
Draining the Pockets
The drainer script routinely executes the malicious contract, immediately draining tokens, NFTs, or stablecoins to an tackle managed by the scammer. Typically, there’s no option to reverse the transaction as soon as it’s confirmed on-chain.
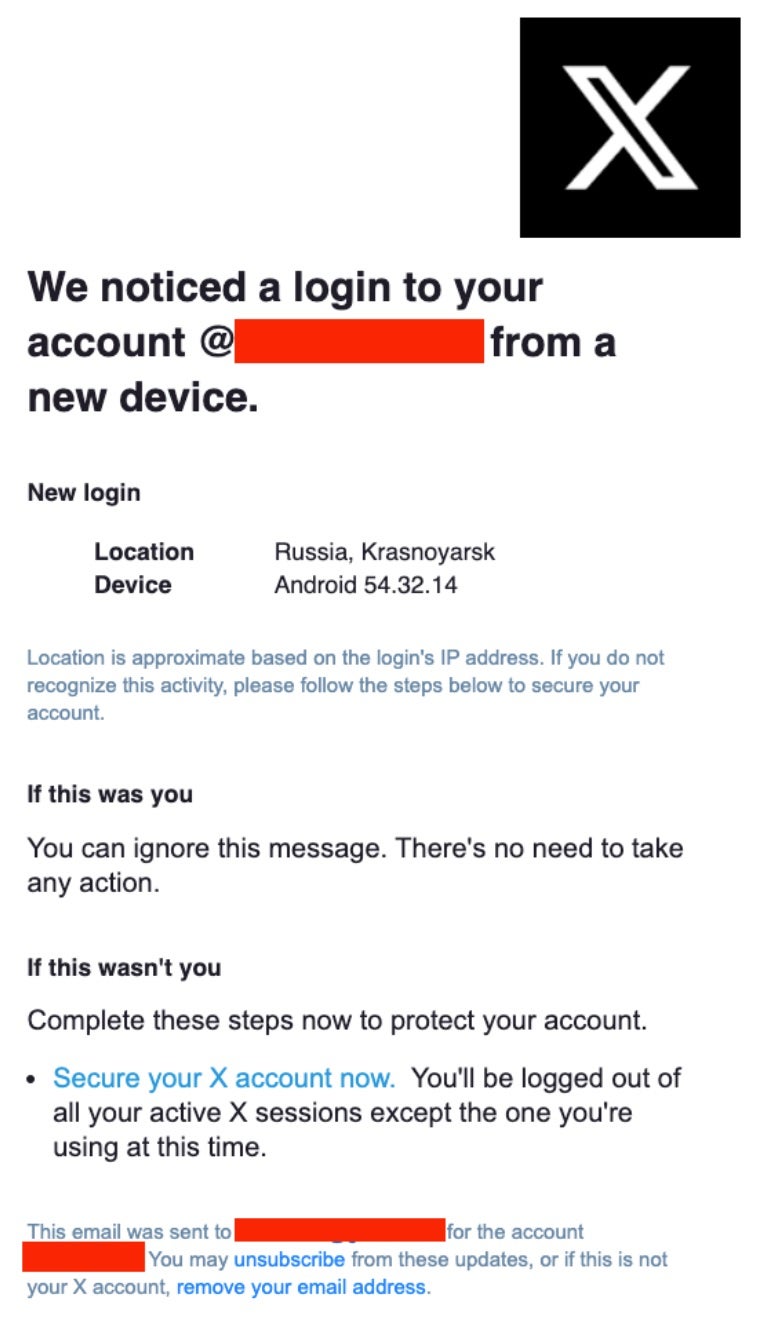
In January 2025, an lively phishing marketing campaign focused high-profile X accounts, together with these of U.S. political figures, journalists, and cryptocurrency organizations. Compromised accounts have been used to advertise fraudulent actions, exploiting the belief of their followers.
Who’s Behind Crypto Drainers-as-a-Service?
This ecosystem includes two essential gamers: expert builders who create and promote drainer kits, and associates or novice scammers who deploy these instruments to steal digital property.
Builders: The Architects of DaaS
Skilled cybercriminals develop refined drainer kits, packaging them with user-friendly interfaces, customizable phishing templates, and automatic scripts. These kits are bought or rented on darkish net boards and Telegram channels. Notable examples embrace:
Angel Drainer: Rising round August 2023, it gives instruments and companies marketed throughout Telegram by identified menace actors. Associates are required to make an preliminary deposit of between $5,000 and $10,000, with operators taking a 20% lower of the stolen funds.
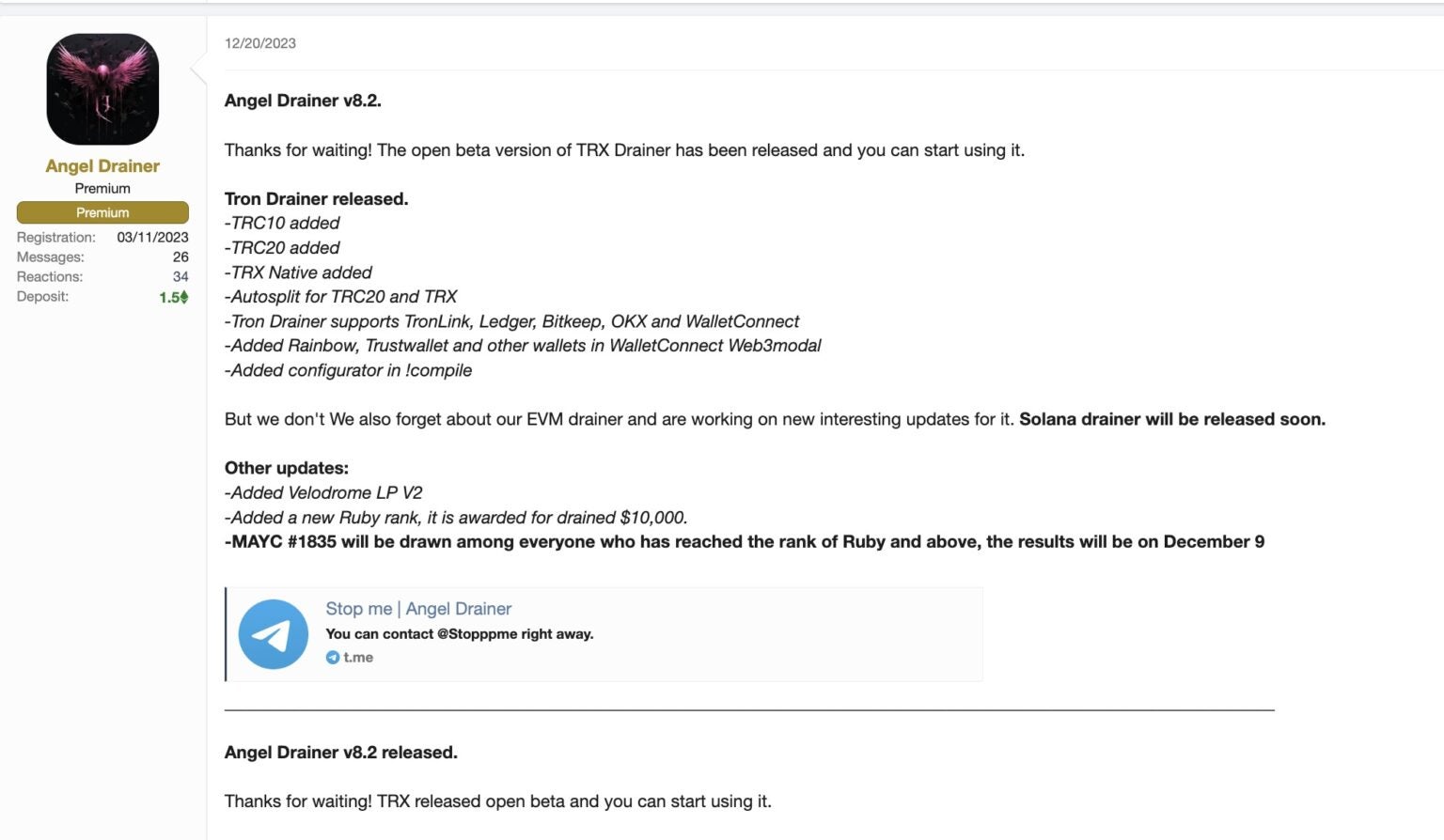
Rugging’s Multi-chain Drainer: Helps 20 totally different crypto platforms and entices associates by providing low charges, round 5-10% of the associates’ positive factors.
These builders usually present common updates to evade detection and should provide buyer help by way of encrypted channels.
Associates: The Executors of Scams
Associates, starting from low-skilled scammers to organized cybercriminal teams, buy or lease these drainer kits to conduct phishing campaigns. They distribute malicious hyperlinks through compromised social media accounts, faux adverts, or direct messages, luring victims to attach their wallets to fraudulent web sites. As soon as a sufferer authorizes a transaction, the drainer script transfers property to the scammer’s pockets.
Monetization Fashions
Crypto Drainers-as-a-Service operators make use of numerous monetization methods:
Subscription Charges: Associates pay a recurring payment for entry to the drainer equipment and related companies.
Income Sharing: Operators take a share (usually 5-25%) of the stolen property. As an illustration, in campaigns utilizing the CLINKSINK drainer, operators took round 20% of the associates’ positive factors.
One-Time Funds: A flat payment grants associates lifetime entry to the drainer equipment.
This commercialized mannequin lowers the barrier to entry for cybercriminals, enabling widespread, coordinated assaults throughout the crypto ecosystem.
Why These Assaults Are Rising
Right here’s a breakdown of why these scams are rising:
Low Barrier to Entry
Crypto Drainers-as-a-Service kits are designed to be user-friendly and require no coding or technical abilities. Even inexperienced scammers can:
Purchase or lease a ready-to-use drainer toolkit.
Customise phishing templates with drag-and-drop interfaces.
Use step-by-step guides offered by builders through Telegram or darkish net boards.
This ease of entry turns anybody into a possible menace actor, fueling the expansion of amateur-driven assaults.
Anonymity and Decentralization
The decentralized nature of crypto permits attackers to maneuver stolen funds with out conventional oversight:
Nameless Wallets: No want for KYC/identification verification means stolen funds are more durable to hint.
Mixers and Cross-Chain Bridges: Instruments like Twister Money or cross-chain bridges are used to launder and obscure stolen crypto.
Lack of Regulation: Various international legal guidelines create loopholes scammers can exploit.
This anonymity incentivizes malicious actors to maintain launching assaults with minimal concern of authorized penalties.
Excessive-Worth, Excessive-Exercise Targets
Because the crypto ecosystem grows, so does the quantity and worth of potential victims:
NFT Drops: Widespread collections appeal to 1000’s of keen consumers, usually tricked into signing malicious contracts on faux mint websites.
DeFi Protocols: Customers usually have giant sums locked in good contracts, making them profitable targets.
Meme Cash and Hype Tokens: These appeal to retail traders who could lack technical know-how and fall for FOMO-driven scams.
Excessive-traffic moments, like trending NFT mints or new token launches, create excellent circumstances for DaaS scams to succeed.
The right way to Defend Your Pockets
DaaS scams have gotten extra refined, making it extra vital than ever to guard your pockets. Right here’s methods to safeguard your property:
Keep away from Connecting to Suspicious dApps
Many scams begin with a phishing hyperlink to a faux dApp. To remain secure:
Double-check URLs earlier than connecting your pockets, particularly throughout NFT drops or token launches.
By no means join your pockets to a dApp shared by way of DMs, sketchy emails, or unknown Discord/Twitter accounts.
Utilizing platforms like Chainabuse or Web3 is Going Simply Nice to test for crypto rip-off experiences.
Use {Hardware} Wallets and Transaction Previews
{Hardware} wallets like Ledger or Trezor preserve your personal keys offline, including an additional layer of safety.
Mix with trusted browser extensions (Rabby or MetaMask) that present transaction previews earlier than you signal.
At all times learn transaction particulars. Crypto Drainers-as-a-Service kits usually cover malicious approvals in deceptive prompts.
Monitor and Revoke Token Permissions
Sensible contracts usually request approval to entry your property indefinitely. Use token approval monitoring instruments to remain in management:
[Insert Image 2]
Evaluation your pockets frequently and revoke entry to dApps you not use.
Keep Knowledgeable
Scammers evolve quick, so ought to your consciousness. To remain forward:
Observe trusted safety accounts like @SlowMist_Team or @CertiK on Twitter/X.
Monitor official channels for dApps and NFT initiatives.
Be a part of communities like r/ethereum, r/CryptoCurrency, or Discord safety channels for real-time crypto rip-off alerts.
By combining these proactive steps, you possibly can dramatically scale back your publicity to Crypto Drainers-as-a-Service scams and different crypto threats. At all times belief your instincts. If one thing feels off, don’t join or signal.
Remaining Ideas
Within the crypto world, staying cautious and practising good pockets hygiene is crucial to defending your property. These scams thrive as a result of they exploit rushed choices and a lack of knowledge. So at all times double-check the websites you go to, scrutinize each pockets permission request, and keep away from connecting your pockets to unknown or suspicious platforms.
Past private vigilance, leveraging obtainable safety instruments can significantly improve your safety. Use {hardware} wallets to maintain your personal keys offline, frequently evaluation and revoke pointless permissions with companies like revoke.money, and keep knowledgeable by way of trusted crypto safety communities.
Keep in mind, in crypto, safety means self-sovereignty; you management your funds, but additionally your dangers. Combining cautious habits with the proper instruments will enable you navigate the crypto area extra safely and confidently. Staying alert, knowledgeable, and vigilant is your finest defence in opposition to scammers. Defend your pockets like your most precious asset, as a result of it really is.
Disclaimer: This text is meant solely for informational functions and shouldn’t be thought-about buying and selling or funding recommendation. Nothing herein needs to be construed as monetary, authorized, or tax recommendation. Buying and selling or investing in cryptocurrencies carries a substantial danger of monetary loss. At all times conduct due diligence.
If you need to learn extra articles like this, go to DeFi Planet and observe us on Twitter, LinkedIn, Fb, Instagram, and CoinMarketCap Neighborhood.
Take management of your crypto portfolio with MARKETS PRO, DeFi Planet’s suite of analytics instruments.”
The publish Crypto Drainers-as-a-Service: How These New-Age Scams Are Focusing on Your Pockets appeared first on DeFi Planet.


