As cryptocurrencies and Web3 platforms develop in reputation, so do the strategies utilized by scammers and hackers to take advantage of customers. Whereas phishing emails, faux token giveaways, and malicious browser extensions as soon as dominated the crypto rip-off house, attackers at the moment are taking a much more invasive and harmful route: counterfeit smartphones.
These faux telephones, typically marketed as high-end Android units at steep reductions, come preloaded with malicious software program designed to steal crypto credentials, drain wallets, or reroute transactions. Not like conventional malware that customers may by accident obtain, these threats are baked into the firmware or pre-installed apps, making them almost not possible to detect or take away.
For Web3 customers and traders, lots of whom depend on cell units to entry wallets, dApps, and exchanges, one of these assault poses a big risk. Even {hardware} wallets and safe apps might be compromised if the underlying machine is contaminated. Because the risk evolves, the necessity for higher consumer consciousness and machine hygiene turns into important.
What Are Faux Telephones?
Faux telephones are units designed to imitate standard manufacturers, corresponding to Samsung, iPhone, or Xiaomi, typically at a fraction of the unique worth. They usually replicate the exterior look and interface of professional fashions, making them onerous to tell apart from real merchandise at first look.
What units these faux telephones aside, and makes them particularly harmful, is what’s hidden beneath the floor. Many include malicious firmware or faux pre-installed apps which are deeply embedded inside the working system. These can steal passwords, personal keys, or crypto pockets knowledge with out the consumer’s data.
As a result of the malware is constructed into the machine itself, even a manufacturing facility reset or antivirus software program could not have the ability to take away the risk. This makes counterfeit telephones a critical cybersecurity threat, significantly for customers concerned in crypto or monetary transactions.
How Crypto Malware Works on Faux Telephones
Faux telephones are sometimes loaded with subtle malware that targets crypto customers from the second the machine is turned on.
Right here’s how the commonest sorts of crypto malware on these units work:
Preloaded Malware
Many counterfeit telephones include built-in malware, rendering them hazardous from the outset. Frequent varieties embrace:
Pockets Drainers: These malicious apps routinely detect crypto pockets exercise and try to switch funds to attacker-controlled addresses.Keyloggers: These secretly report all the things you kind, together with seed phrases, passwords, and PINs, then transmit the information to distant servers.Clipboard Hijackers: Once you copy a pockets deal with to make a transaction, the malware swaps it with the attacker’s deal with, tricking you into sending funds to the unsuitable recipient.Faux Pockets Apps: These mimic standard wallets, corresponding to MetaMask or Belief Pockets, however are designed solely to seize login credentials or seed phrases.
Backdoors and Distant Entry
Some faux telephones include built-in backdoors, permitting attackers to:
Entry the machine remotelySet up further malwareExport your personal keys or pockets knowledge with none consumer immediate
This implies attackers may steal your funds even in the event you by no means knowingly obtain something malicious.
Faux System Updates
To keep up management, attackers typically disguise malicious code as professional system updates. These faux updates could seem as Android system messages or pop-ups. When accepted, they set up much more malware or improve current surveillance instruments with out consumer consent.
Mimicking Legit Wallets
Fraudulent apps could appear and feel precisely like trusted wallets corresponding to MetaMask, Phantom, or Belief Pockets. These clones are sometimes indistinguishable to the untrained eye however are programmed to phish your credentials or misdirect transactions the second you enter your seed phrase.
Distribution Techniques: How Hackers Promote Counterfeit Telephones
Hackers and cybercriminals have grow to be more and more subtle in how they distribute counterfeit telephones embedded with crypto malware. These units are sometimes offered by way of faux e-commerce platforms that imitate professional retailers, full with faux critiques, professional-looking layouts, and deep reductions to lure unsuspecting patrons.
These web sites could disappear after a brief interval, making it onerous to hint the sellers or demand refunds.
One other standard distribution methodology is peer-to-peer marketplaces, corresponding to Craigslist, Fb Market, or Telegram channels. Right here, sellers pose as people providing “gently used” or “unopened” telephones, typically claiming they’re imported, “manufacturing facility unlocked,” or uncommon “restricted editions.” These offers are normally priced nicely under market worth to tempt cut price hunters, particularly in areas the place official units are costly or onerous to seek out.
Shady resellers or small tech retailers working in unofficial retail zones additionally play a job in pushing these counterfeit units. These distributors could combine faux telephones with actual inventory, making it troublesome for a median purchaser to identify the distinction. The packaging, branding, and interface typically seem professional at first look, rising the chance of the telephone being trusted and used for delicate functions corresponding to crypto wallets.
Hackers deliberately goal areas with excessive crypto adoption however comparatively weak shopper protections and tech regulation, corresponding to components of Southeast Asia, Africa, and Latin America. In these areas, the mixture of excessive cell phone demand and restricted enforcement makes it simpler to flood the market with compromised units. The tip purpose is straightforward: achieve distant entry to victims’ wallets and drain their funds with out detection.
Tips on how to Shield Your self from Faux Telephone Crypto Scams
As counterfeit telephones with embedded crypto malware grow to be extra subtle, it’s essential for Web3 customers and crypto traders to undertake proactive defences.
Listed here are key methods to guard your self from these high-risk scams:
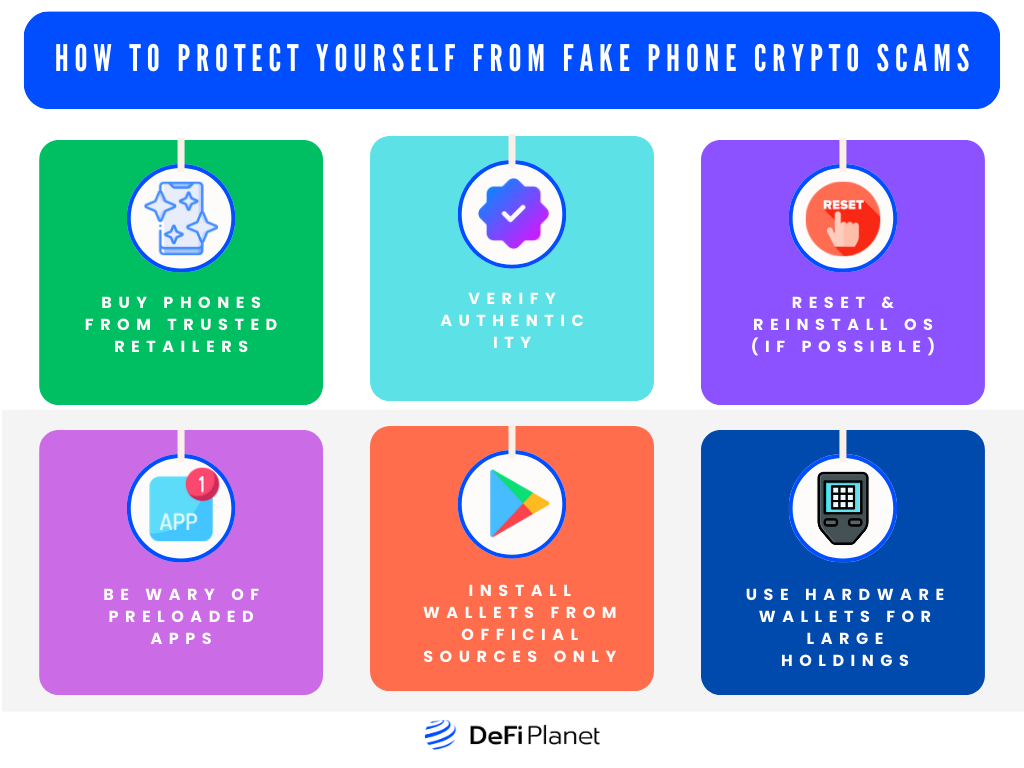
Purchase Telephones from Trusted Retailers
To keep away from falling sufferer to faux telephone crypto scams, all the time purchase your units from trusted and approved retailers. Buying smartphones immediately from official model shops or their licensed companions ensures that you simply obtain a real product free from hidden malware.
Alternatively, gray-market sellers, on-line third-party distributors, and unknown social media resellers could supply units at attractive costs, however these typically include vital dangers, particularly for these coping with digital property.
Confirm Authenticity
After shopping for a brand new telephone, verifying its authenticity is crucial. Use official instruments supplied by manufacturers like Apple, Samsung, or Xiaomi to verify that your machine is real. Examine the packaging intently, look out for poor brand printing or uncommon design options, and check the construct high quality.
You must also verify the IMEI and serial numbers by dialling *#06# and evaluating them on the producer’s official web site. These easy checks can reveal whether or not your machine is counterfeit or compromised.
Reset & Reinstall OS (If Potential)
When you’ve got any doubts a couple of telephone’s origin, particularly if it got here from an unofficial supply, it’s essential to wipe the machine clear. Performing a full manufacturing facility reset is step one, however for larger safety, reinstall the unique working system utilizing firmware from the official model web site.
This course of helps take away any malicious code embedded in system-level functions or firmware that could possibly be used to steal crypto property.
Be Cautious of Preloaded Apps
One main pink flag on counterfeit telephones is the presence of suspicious or unfamiliar apps that come pre-installed. These apps could seem innocent, however they might really perform as wallet-draining malware, keyloggers, or distant entry instruments.
As quickly as you arrange your machine, take the time to evaluation all put in functions and take away something that appears misplaced or pointless. Apps with imprecise descriptions or extreme permissions needs to be deleted instantly to cut back the danger of compromise.
Set up Wallets from Official Sources Solely
In no way must you belief any crypto pockets app that comes pre-installed on a tool. To make sure your digital property stay safe, all the time set up wallets immediately from official app shops such because the Apple App Retailer or Google Play Retailer.
Follow well-known suppliers like MetaMask, Belief Pockets, or Phantom, and confirm the writer and app critiques to keep away from downloading faux or malicious variations. This further step will help defend you from apps designed to steal your personal keys or credentials.
Use {Hardware} Wallets for Giant Holdings
For these holding vital quantities of cryptocurrency, counting on cell wallets, even on trusted units, can nonetheless pose pointless dangers. A {hardware} pockets offers a safer, offline methodology for storing your personal keys and crypto property.
By maintaining your holdings off of internet-connected units, you enormously scale back your publicity to hacks, malware, or backdoors. That is essential in at present’s surroundings, the place faux telephones are being engineered particularly to take advantage of mobile-based wallets.
Remaining Ideas
Because the crypto business continues to develop, so does the complexity and scale of the threats focusing on customers. Counterfeit telephones loaded with crypto-draining malware characterize a brand new and harmful frontier in cybercrime, one the place even your {hardware} can’t be trusted. These assaults are stealthy, onerous to detect, and sometimes irreversible as soon as funds are stolen.
The perfect defence is vigilance. All the time confirm the authenticity of your units, keep away from utilizing preloaded apps for something associated to crypto, and educate others in your group concerning the dangers. By staying knowledgeable and cautious, you may get pleasure from the advantages of Web3 whereas maintaining your property protected from evolving threats.
Disclaimer: This text is meant solely for informational functions and shouldn’t be thought of buying and selling or funding recommendation. Nothing herein needs to be construed as monetary, authorized, or tax recommendation. Buying and selling or investing in cryptocurrencies carries a substantial threat of monetary loss. All the time conduct due diligence.
If you need to learn extra articles like this, go to DeFi Planet and observe us on Twitter, LinkedIn, Fb, Instagram, and CoinMarketCap Group.
Take management of your crypto portfolio with MARKETS PRO, DeFi Planet’s suite of analytics instruments.”


