Not all crypto losses come from hacks or faux wallets. Some come from design decisions hidden in sensible contracts. These setups enable entries however block exits—like a entice that solely closes when you step inside.
These scams are sometimes referred to as honeypots. They appear regular, really feel secure, and behave like actual tasks till you attempt to depart. This information explains how honeypots work, frequent warning indicators, and tips on how to shield your self.
What Is a Honeypot Crypto Rip-off?
A honeypot crypto rip-off is a kind of crypto fraud designed to entice you: it’s constructed to ask in deposits, then block exits.
Scammers promote these traps as engaging funding alternatives and create urgency.
It’s a misleading scheme the place the whole lot appears to be like actual at first. The token, web site, and exercise all seem reliable, usually copying reliable tasks you could already belief. You should purchase the token, however you can not promote it. That design causes direct monetary loss as soon as your funds get caught.
Honeypots succeed as a result of they exploit belief, velocity, and primary buying and selling habits. If you happen to ever work together with out correct due diligence, you danger falling sufferer to it, too.
How Honeypot Crypto Scams Work
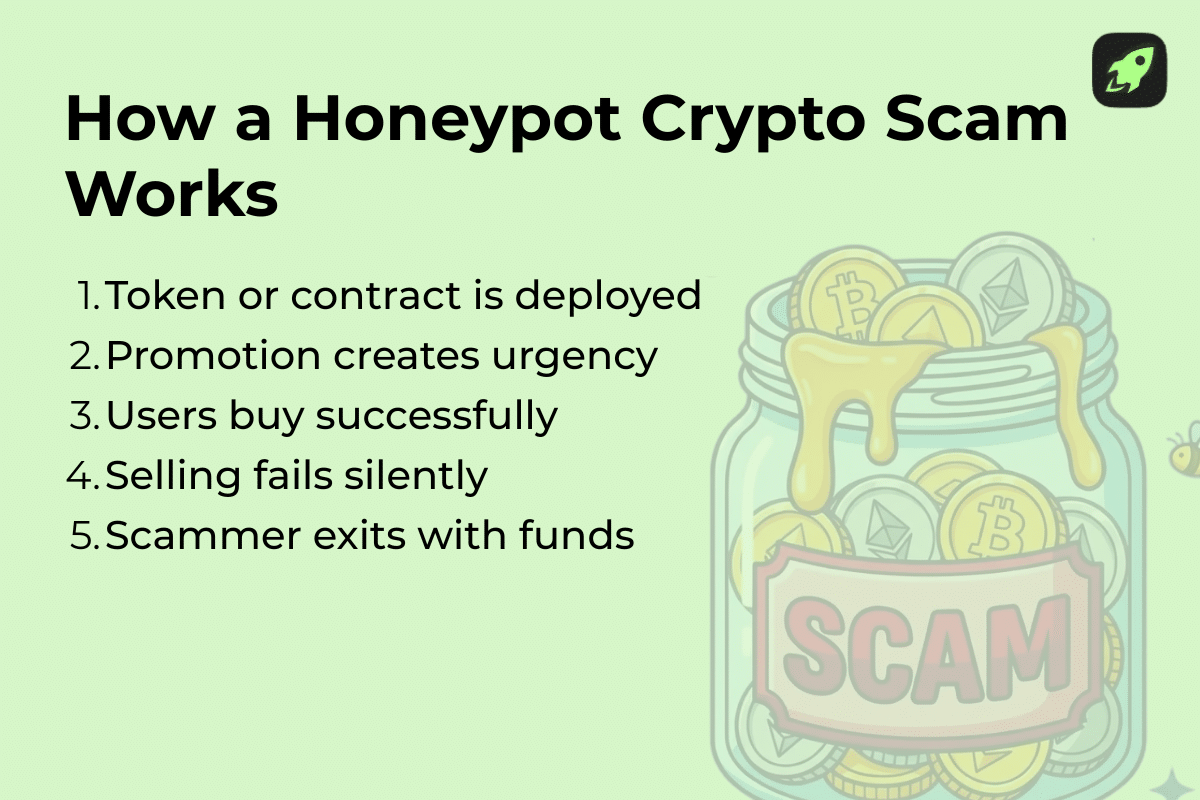
Honeypot assaults observe a repeatable sample. Scammers design traps that look secure and acquainted. They lure traders in with worthwhile guarantees and urgency. As soon as an unsuspecting sufferer interacts, they quietly lose management of their funding.
1. Creation of a Faux Token or Good Contract
Initially deployed on Ethereum, these methods now seem throughout EVM-based networks.
The rip-off begins with a malicious sensible contract that hides its restrictions. It behaves like a normal Ethereum sensible contract, a sample frequent throughout the Ethereum community and different EVM-compatible chains.
Scammers situation a local token that appears tradable. Its on-chain information seems actual. However the token continues to be faux by design.
When the sufferer interacts, the contract permits shopping for however silently blocks promoting.
2. Attracting Traders with Guarantees
Scammers then drive consideration to the rip-off. They promote the token throughout social media platforms utilizing coordinated social media campaigns. Some posts declare faux partnerships or staged celeb endorsements. Such early ‘exercise’ makes the token look common and prefer it’s gaining traction. New customers see motion and rush in. The pitch frames the rip-off as unique funding alternatives with a restricted time window.
3. The Lure: Deposit, however No Withdrawal
Shopping for works with out points. Promoting fails.
Error messages usually blame gasoline charges or community issues, however the fact is that the contract is programmed to forestall withdrawals.
You verify the pockets tackle. Every little thing appears to be like appropriate. You by no means shared your personal key, but the funds stay locked. This conduct is a transparent pink flag: the setup almost certainly funnels liquidity right into a single permissioned promote tackle.
4. Scammer Cashes Out
As soon as sufficient liquidity builds, the scammer’s pockets prompts. Dangerous actors use automated instruments like sweeper bots to ‘sweep’ funds: belongings are instantly transferred to a 3rd pockets. Your funds disappear, whereas scammers exit quietly. This closing stage ends the operation and leaves you with no restoration path.
Sorts of Honeypot Crypto Scams
The setup varies, however the objective stays the identical: honeypot assaults finally lock your funds whereas trying secure. Each model has a nasty actor abusing belief, velocity, and poor checks. Under are the most typical sorts you’ll encounter.
1. Good Contract-Based mostly Honeypots
This kind depends on a malicious sensible contract. These scams dominate Ethereum-based tokens as a result of anybody can deploy contracts shortly.
The code permits for purchase performance however quietly restricts exits. An tackle blacklist lets the deployer determine who can promote.
Scammers automate the entice utilizing automated scripts to cover the restrictions. The exploit stays invisible to informal customers. When you work together, the attacker controls outcomes.
2. Liquidity Honeypots
Liquidity honeypots abuse liquidity swimming pools on an automatic market maker. You may add funds and commerce in, however exits fail. Scammers might route trades via decentralized exchanges to look secure. Behind the scenes, contract logic or pool guidelines stop withdrawals. Charts transfer, quantity seems actual, however liquidity solely flows a technique.
3. Ponzi Scheme Integration
Some honeypots mix with Ponzi-style mechanics. These misleading schemes promise rewards for early customers. Scammers lure traders by paying early individuals with later deposits. The construction collapses as soon as inflows gradual. At that time, trapped funds stay locked, whereas the scammer exits.
4. Faux Airdrops
Faux airdrops goal curiosity and greed. Scammers promote free tokens that look faux solely after the harm is completed. You’re requested to attach your pockets or signal a transaction. This doesn’t expose personal keys, however can approve malicious contract actions. In consequence, the interplay can silently grant spending permissions or execution rights.
The rip-off operates on an actual community, which provides credibility. No funds arrive, however entry will get compromised.
5. False ICO or Token Sale Scams
These scams copy early token launches. They promote unique funding alternatives tied to recognized manufacturers. Web sites mimic reliable tasks and declare backing from a reliable firm. Some tasks even depend on paid actor advertising to simulate natural curiosity. However as soon as gross sales finish, tokens lock or disappear. Patrons are left holding belongings they can’t promote.
6. Faux DeFi Protocols
Faux DeFi protocols are constructed to seem like an actual system you may belief. The interface feels full and purposeful. Deposits work with out points. Rewards seem on-screen. Behind the scenes, nevertheless, the platform operates as a honeypot system. When you deposit funds, withdrawals cease. Errors seem or transactions fail silently. By the point you notice what’s occurred, management already belongs to the scammer.
Some Honeypot Applied sciences
Honeypots didn’t begin in crypto. They really come from cybersecurity. Safety groups use them to check assaults with out risking actual belongings. Scammers simply borrowed the identical concepts and reversed the objective. As a substitute of learning attackers, they entice customers. Understanding these applied sciences helps you see how crypto honeypots are designed.
At a primary stage, honeypots exist to lure attackers into interacting with one thing that appears beneficial. The system information conduct and exploits belief. In crypto scams, in the meantime, you turn into the goal as a substitute of the attacker.
Shopper Honeypots
Shopper honeypots simulate regular consumer conduct. They work together with web sites, apps, and contracts mechanically. Safety groups pair them with intrusion detection programs to catch actual threats. This setup creates fewer false positives than passive monitoring. Scammers adapt this logic to observe how customers commerce, signal, and approve transactions.
Malware Honeypots
Malware honeypots exist to watch malware assaults in a managed approach. They gather information on how malicious code spreads, triggers, and executes. Safety groups use this to grasp assault patterns and enhance defenses.
Crypto scammers reuse the identical logic: They monitor how wallets work together, which approvals succeed, and the place customers hesitate. This suggestions helps scammers refine scripts that drain wallets, block withdrawals, or set off solely after particular actions. Over time, the rip-off turns into tougher to detect as a result of it adapts to consumer conduct.
Honeynets
Honeynets are teams of linked traps. They seem like lively environments, not single decoys. They usually connect with different programs to look life like. Some even resemble an actual system with ongoing exercise. This realism will increase belief and retains victims engaged longer.
Database Honeypots
A database honeypot focuses on saved worth. Its objective is to acquire data from anybody who interacts with it. These programs usually comprise faux however life like delicate data.
In crypto scams, this method targets pockets approvals, signatures, or personal metadata. Chances are you’ll be requested to approve a transaction that appears innocent. That approval can grant ongoing entry to your funds. As soon as signed, the scammer can act with out asking once more.
Low- vs. Excessive-Interplay Honeypots
Low-interaction honeypots provide restricted capabilities and gather primary information.
A high-interaction honeypot behaves nearly like an actual product.
In crypto, high-interaction traps trigger essentially the most harm as a result of the whole lot seems regular. You may commerce, stake, or declare rewards with out errors for a very long time, however while you lastly attempt to withdraw, the contract blocks you and locks your funds.
Actual Examples
Squid Recreation (SQUID) Token Rip-off, 2021
In late October 2021, a fraudulent token referred to as Squid Recreation (SQUID) exploded in recognition after launching on Binance Good Chain. It claimed to be tied to a play-to-earn sport impressed by the hit Netflix present Squid Recreation.
The worth surged by 1000’s of % in days. Traders raced in, hoping for fast positive factors.
Then, many found that they may not promote their tokens: gross sales have been technically blocked by a promote restriction within the sensible contract. Inside hours, builders withdrew liquidity and vanished. The token value crashed to just about zero, and victims misplaced thousands and thousands of {dollars}. This stays some of the notorious crypto honeypot scams of the Web3 period.
Dechat PancakeSwap Honeypot Incident, 2024
In February 2024, the Dechat mission mistakenly linked a honeypot token in an official announcement.
This error on PancakeSwap directed customers to a entice token as a substitute of the reliable contract. Traders tried to work together, considering they have been participating with an actual mission, solely to seek out their funds locked.
Recurring Refined Honeypot Campaigns, 2024
Blockchain safety agency Hacken reported that in early 2024, a single attacker executed a number of honeypot scams totaling about $3.2 million in stolen funds.
These assaults used misleading sensible contracts with hidden mechanisms that both blocked withdrawals or drained sufferer belongings after interplay. They have been promoted via varied channels, together with Telegram and crypto boards, utilizing coordinated ways that resembled low-effort promotions, and ended up inflicting actual harm.
Widespread Traits of Honeypot Crypto Scams
Honeypot crypto scams all share the identical construction. You may spot them early if you already know the place to look.
The primary pink flag is lacking or unclear promoting guidelines. The mission explains tips on how to purchase, not tips on how to exit.
As you dig deeper, alerts stack up:
Contracts conceal permissions
Liquidity sits in a single pockets
Groups keep away from direct solutions
Advertising pushes urgency as a substitute of details
If you ignore these indicators, the result’s predictable monetary loss.
The right way to Shield Your self
You shield your self by slowing down and checking the fundamentals. To keep away from falling sufferer to those scams, assume nothing is secure by default. Each commerce wants due diligence. Meaning studying the foundations, not trusting the hype. Robust safety habits make it easier to determine dangers early, earlier than cash leaves your pockets.
If you would like a sensible instrument for every day use, we’ve created a brief anti-scam guidelines PDF. It covers the most typical warning indicators and determination checks earlier than you click on, join, or ship. Drop your electronic mail tackle beneath and we’ll ship it your approach.
Keep Secure within the Crypto World
Discover ways to spot scams and shield your crypto with our free guidelines.

Pink Flags in Token Contracts
Begin with the code. Many scams depend on a malicious sensible contract that hides promoting limits. Search for restrictions on transfers or promoting.
Watch out even on trusted manufacturing programs just like the Ethereum mainnet, Binance Good Chain, or Polygon. A rip-off can run on a dwell community with actual customers and actual quantity. Community legitimacy doesn’t equal mission security.
Official tasks will usually publish sensible contract audits from recognized companies. Follow reliable firm audits with public reviews.
Indicators in Liquidity Swimming pools and Exchanges
Subsequent, research buying and selling circumstances. At all times verify how buying and selling really works.
Begin with liquidity swimming pools. Take a look at who supplies the liquidity. If one pockets controls most of it, you rely on that pockets’s conduct. That’s an actual danger.
Then verify crypto alternate exercise. Sudden value spikes and not using a lengthy historical past ought to gradual you down. Quick pumps appeal to consideration, not stability.
Subsequent, open the transaction historical past. Scroll for a minute. Do you see actual sells, or solely buys? When shopping for works however promoting barely occurs, one thing’s flawed. One-way trades usually generate faux liquidity alerts, indicating the exits are blocked by design. If promoting works for some wallets solely, an tackle whitelist could also be lively.
If buying and selling feels one-directional, belief that feeling. Markets want exits. When exits disappear, security disappears with them.
Warning Indicators in Advertising and Social Media
Now have a look at how the mission talks to you.
Scammers push velocity. They flood social media platforms with urgency and guarantees. Aggressive social media campaigns give attention to value, and never on the product.
Be further cautious with celeb endorsements. YouTube, X, Reddit, and Discord are flooded with faux promotions and AI-generated deepfakes pushing shady tasks. Screenshots, reposts, or imprecise shout-outs show nothing. Anybody can faux a point out or pay for publicity.
Actual groups publish clear documentation, clarify dangers, and reply onerous questions. Scams keep away from particulars and rush you to behave.
Instruments for Contract and Token Evaluation
You don’t want coding abilities to confirm claims your self.
Instruments like Token Sniffer scan contracts mechanically. They flag blocked sells, hidden taxes, and dangerous permissions. This helps you see issues earlier than you work together. Deal with warnings severely, even when hype appears to be like robust.
Blockchain explorers equivalent to Etherscan and BscScan present actual on-chain exercise. Open a block explorer to overview holders, transaction flows, and contract controls. This information reveals who holds energy and whether or not actual customers can promote.
These checks reveal who controls the token and the way it behaves. Be taught extra about tips on how to keep secure in crypto in our devoted information.
What to Do If You’re Trapped in a Honeypot
If you happen to hit a honeypot, deal with it as a safety incident. It’s essential act shortly however calmly.
Cease interacting with the contract.
Don’t approve new transactions.
Revoke current permissions.
Switch secure belongings to a brand new pockets.
Doc what occurred.
Watch out with restoration providers. Many promise assist however can’t really reverse sensible contracts. Typically, the locked quantity can’t be recovered. It helps to simply accept that early and shift your focus. Shield what you have got left, safe your pockets, and keep away from making the scenario worse.
Last Ideas
Honeypots work as a result of they mix in. They seem like some other token at first. That’s why a skeptical mindset helps. When particulars about promoting are lacking or unclear, pause. A couple of minutes of due diligence usually stop weeks of frustration later.
FAQ
How is a honeypot rip-off totally different from a rug pull?
Honeypot scams entice you on the contract stage. You should purchase, however promoting fails by design. A rug pull works in a different way. Builders take away liquidity after launch. Each exploit belief, however honeypots block exits from the beginning. Rug pulls collapse all of the sudden. Honeypots lock you in quietly.
Can I recuperate my funds if I fall for a honeypot rip-off?
No, you normally can’t recuperate funds misplaced to a honeypot. Good contracts execute as written. There isn’t a reversal. Regulation enforcement hardly ever helps on account of jurisdiction limitations. Settle for the monetary loss and give attention to prevention. Restoration providers promising refunds are sometimes additionally scams.
What instruments can I take advantage of to detect honeypot scams earlier than investing?
Instruments like Token Sniffer can flag blocked sells and dangerous permissions. Blockchain explorers can affirm actual buying and selling exercise. Keep in mind that reliable tasks publish audits and permit contract supply verification. These checks take minutes and forestall costly errors.
Disclaimer: Please notice that the contents of this text aren’t monetary or investing recommendation. The data offered on this article is the writer’s opinion solely and shouldn’t be thought-about as providing buying and selling or investing suggestions. We don’t make any warranties in regards to the completeness, reliability and accuracy of this data. The cryptocurrency market suffers from excessive volatility and occasional arbitrary actions. Any investor, dealer, or common crypto customers ought to analysis a number of viewpoints and be conversant in all native rules earlier than committing to an funding.


